demystifying series
What is Endpoint Detection and Response (EDR) ?
BREAKING DOWN THE BASICS
Secure IT EDR is a crucial layer of threat detection that safeguards endpoint technology such as laptops, desktops, tablets, and even high-end computing equipment like servers. However, there are often questions surrounding EDR. For instance, can an EDR solution prevent ransomware and phishing attacks, or is it too basic for my organization’s needs?
EDR is an emerging solution in the security space, and this article aims to answer these pressing questions about EDR and more.
What is EDR?
EDR, or Endpoint Detection and Response, is a security-as-a-service solution that focuses on endpoint devices such as laptops, desktops, or tablets. These devices are continuously monitored by the EDR solution to detect and respond to cyber threats like ransomware and malware.
 Endpoint computing is often the entry point for attackers and users who need to access the organization’s network for their daily tasks. A hacker can exploit a user’s endpoint device to gain unauthorized access to the network, especially when the user loads non-compliant applications or visits websites that produce malicious code. Outdated or missing patches on these endpoints and applications can also expose the device to vulnerabilities.
Endpoint computing is often the entry point for attackers and users who need to access the organization’s network for their daily tasks. A hacker can exploit a user’s endpoint device to gain unauthorized access to the network, especially when the user loads non-compliant applications or visits websites that produce malicious code. Outdated or missing patches on these endpoints and applications can also expose the device to vulnerabilities.
What problems does an EDR solution solve?
EDR solves several security-related problems.
It provides continuous monitoring and protection of endpoint devices, detects and responds to threats in real-time, prevents data breaches, and improves the overall security posture of the organization.
Is it more than just point product like anti-virus?
Yes!
An EDR solution combines various technologies to provide advanced threat protection. It also includes live agent monitoring, something a point product will never have. This human layer of protection provides constant updates while looking out for security threats.
How does EDR work?
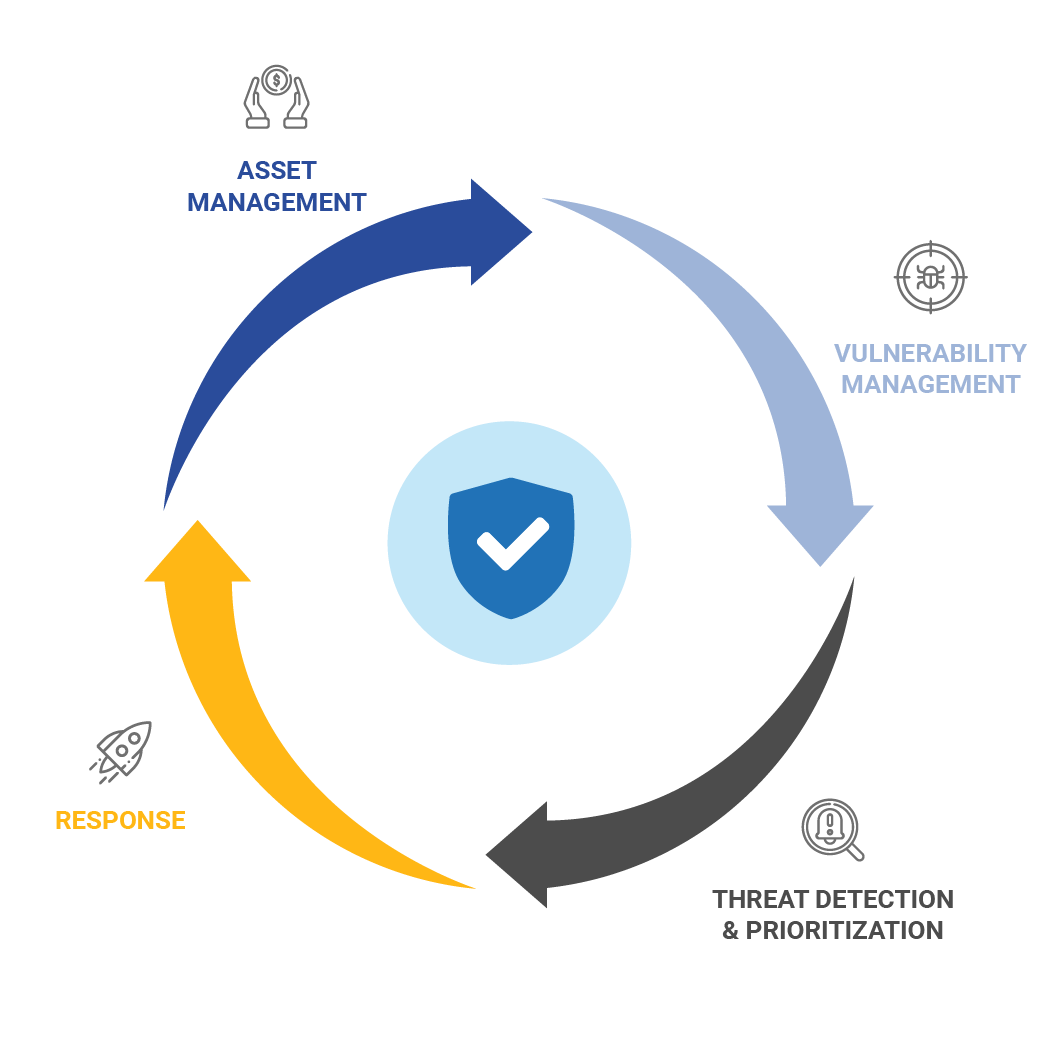
EDR comes with a deployment team that assesses, designs, and deploys the EDR solution to your endpoints using advanced security policies and processes. These processes provide dynamic application containment, real-time protection, active threat protection, and advanced security integration with a Security Incident and Event Management (SIEM) system. The SIEM uses state-of-the-art machine learning to determine if a threat is occurring within your environment.
What are the benefits of investing in an EDR solution?
Regardless of the size of your organization, it’s crucial to protect your data, assets, people, and reputation. EDR provides always-on security protection featuring threat defense. It’s more than just asset protection; it’s also a threat hunter, keeping your organization ahead of live active threats.
With EDR, you get advanced endpoint protection for all devices, plus live agent monitoring. This extra layer of human protection is often overlooked in security protection discussions. EDR is also a round-the-clock service managed by a team of highly trained network and security specialists. This means all your important updates are done in real-time, improving your security posture while identifying and preventing active threats to your business.
What would happen to my organization if I did not have an EDR solution?
Without an EDR solution, your company could be left in limbo or even face closure. That’s how serious a data breach can be for any size organization.
According to the most recent IBM Data Breach Report:
%
of organizations believe a data breach is imminent
%
of organizations already experienced a major data breach
This uncertainty has led many to embrace new forms of security such as EDR. Another important development is that the chances of a second data breach become higher after the first.
million U.S. dollars is the average cost of a data breach in the U.S.
million U.S. dollars is the average cost of a data breach globally
Data breaches cost money, time, and significantly impact the overall effectiveness of the organization. No one can afford a hit like this.
Do I still need an anti-virus or DLP with EDR?
No!
An EDR solution has all the best anti-virus technology available. As for DLP or data loss prevention technology, that’s exactly what EDR handles. The case here for EDR is that it’s a full solution over point solutions, which is what DLP, and anti-virus are. Plus, EDR comes with a SIEM as part of the package providing organizations with a sophisticated approach to hunt down and track possible threats before they happen. SIEM technology was, at one time so expensive that it was only possible for banks and Fortune 500 organizations to afford them, but with EDR any size organization can get security events analyzed and their entire environment protected.
What security solution can I get started with to protect my organization from ransomware and malware?
This may be hard to believe but ransomware attacks take longer to remediate than data breaches according to the 2022 Cost of a Data Breach report released by IBM. These criminal organizations have gotten smarter and have insights into your business and will more than likely strike again. With EDR the most important aspect of the solution when it comes to ransomware is the “detection” part.
A solution such as Secure IT™ – EDR provides advanced, comprehensive threat detection for users on laptops, desktops, tablet devices and mobile phones. EDR is a fully managed and monitored solution meaning the security posture gets checked and improved upon in real-time by subject matter experts that can deploy, configure, maintain, and respond to any endpoint threat. The chances are that if a ransomware attack occurs will be funneled through hardware devices making EDR vital in any organization.
What makes Jolera’s Secure IT (EDR) different?
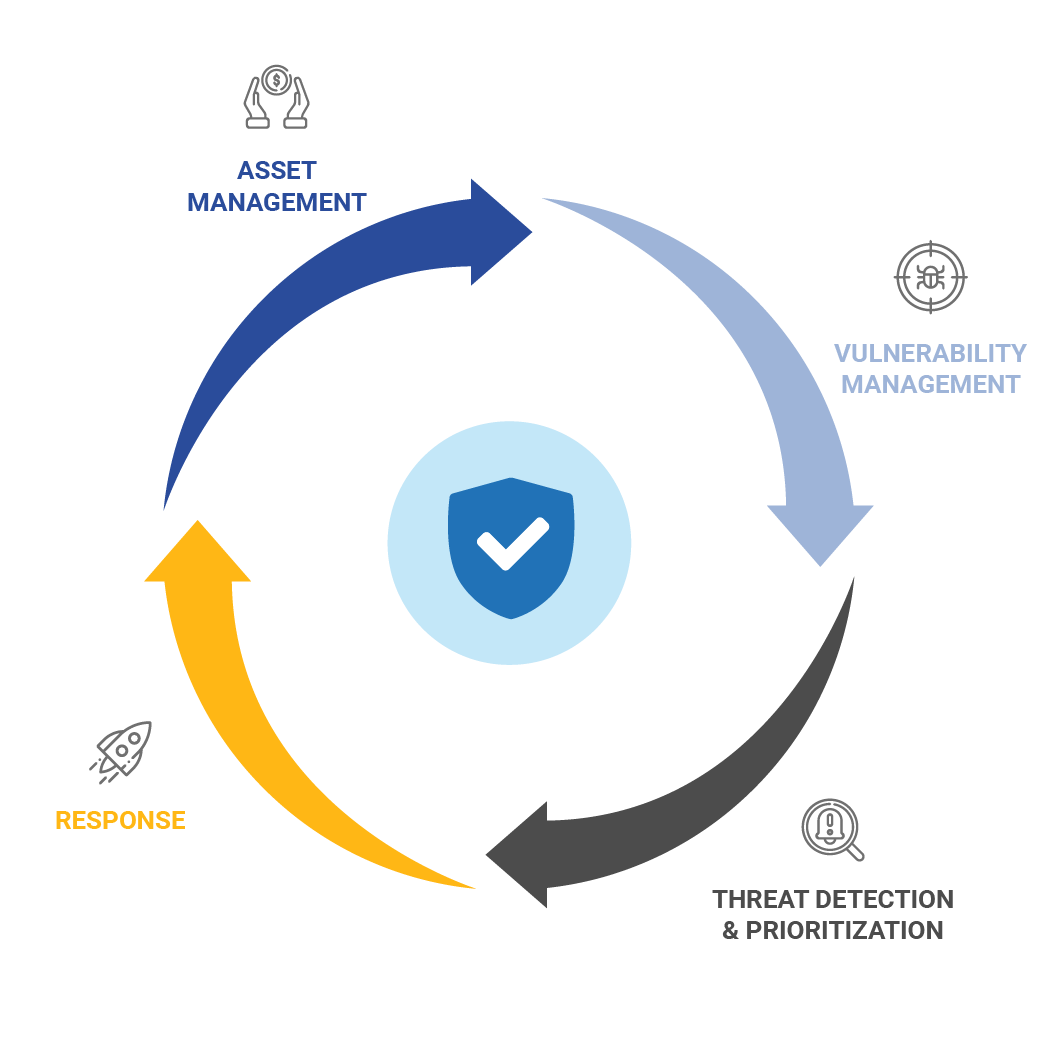
Jolera’s Secure IT™ Endpoint Detection and Response, powered by SentinelOne, offers a cutting-edge solution for endpoint protection by preventing, detecting and acting on ever-changing threats. This solution works at hyper-speed as it provides quick recovery when exploitation, such as ransomware, occurs.
Secure IT EDR covers all your bases as it offers resource-efficient autonomous agents for Windows, Mac, Linux and Kubernetes along with supporting various form factors, including physical, virtual, VDI, customer data centers, hybrid data centers, and cloud service providers.
Secure IT EDR is not a point product as it also features a team of network and security specialists monitoring the environment for incidents and threats actors around the clock.
The centrally managed solution also comes with state-of-the-art data-driven dashboards and analytics providing valuable real time insights and access to the health of all your endpoints along with its security posture.
Covers All Bases
Windows, Mac, Linux and Kubernetes
Various Form Factors
Physical, virtual, VDI, customer data centers, hybrid data centers, and cloud service providers
24/7/365 Globally
Network and security specialists monitoring the environment for incidents and threats actors
data-driven insights
State-of-the-art data-driven reports and analytics providing valuable real-time insights
dashboards
Access to the health of all your endpoints along with its security posture
How do I know or trust that all my end users and devices are continuously monitored to prevent cyber-attacks?

monthly report

Network Operations Centre
End-user security reviews
There are several ways that confirm this from the automatically generated monthly report, which allows the organization to view and fully understand the security posture along with the threat vectors detected to the Security Operations Centre team that works around the clock to detect and fight against active threats.
But there is more such as the Network Operations Centre team that comprises live agents who monitor all devices on the network, while performing alerts within the infrastructure.
Finally, there is end-user security reviews and analysis available to the organizations.
Should I worry that Endpoint is too entry level for my organization?
If it was just an anti-virus, then yes! The hacker community is way too sophisticated, talented, and organized to back off from just anti-virus.
EDR includes anti-virus but comes with so much more, such as:
– exploit prevention
– desktop firewall
– sandboxing
– malware protection
– application containment
– integrated machine learning
EDR is not an entry-level solution when you compare it to a point product such as an anti-virus. EDR is a fully monitored and managed solution that helps organizations dramatically improve their overall security posture in a cost-effective manner.
Is EDR strong enough to protect remote and on-the-cloud workers?
Yes!
EDR is designed to protect all endpoints, regardless of their location. Whether your employees are working remotely or on the cloud, EDR provides continuous monitoring and protection against cyber threats.
How will an EDR solution help with internal threats for my organization? Is EDR only for external threats?
EDR is designed to handle both internal and external threats.
It continuously monitors all activities on the endpoint devices and can detect unusual or suspicious behavior, whether it originates from inside or outside the organization.
Should an MSP have EDR as part of its portfolio of solutions?
Yes!
As an MSP, having EDR as part of your portfolio of solutions can significantly enhance the security services you offer to your clients. It provides a comprehensive and advanced security solution that can protect against a wide range of cyber threats.
Conclusion
Jolera’s Secure IT™ Endpoint Detection and Response (EDR), powered by SentinelOne, provides robust and cutting-edge security for diverse endpoint environments. With features such as real-time threat prevention, detection, and autonomous response capabilities, it offers superior protection against an evolving threat landscape.
Accommodating various workstation environments, including Windows, Mac, Linux, and Kubernetes, it supports physical, virtual, VDI, and hybrid data centers, along with cloud service providers. Underpinned by the dedicated support of our Global Intelligence Response Center (GIRC) team of cyber threat experts, Secure IT™ EDR empowers organizations to maintain control over their cybersecurity, minimize risks, and protect their critical digital endpoints.

