by Jolera | Jul 20, 2022 | IT News
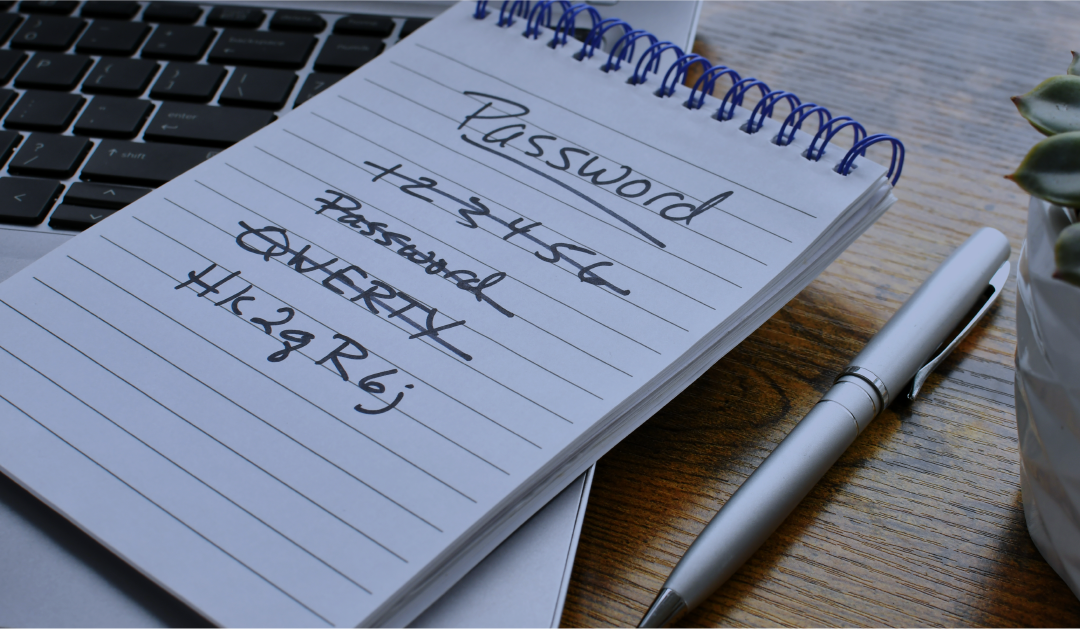
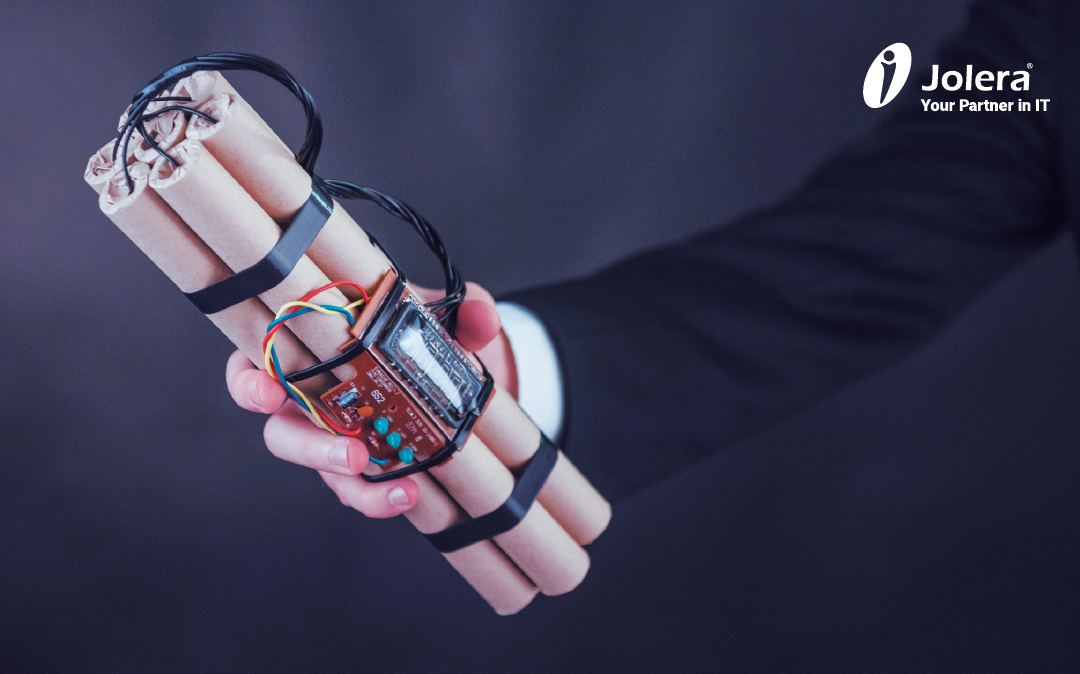
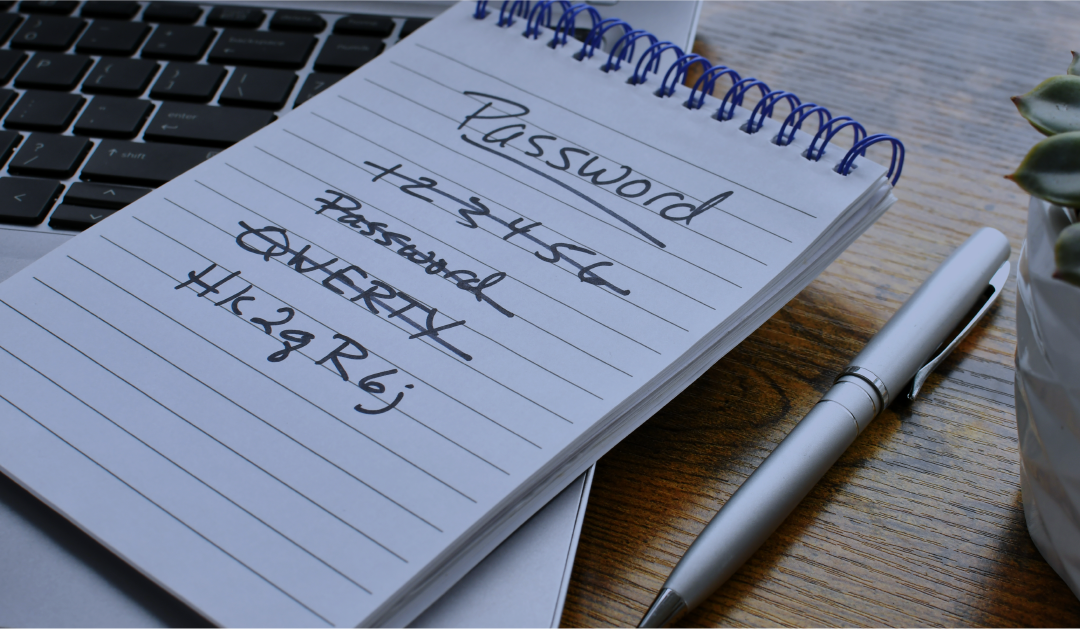
How a new Azure MFA Enablement service from Jolera can better protect users and organizations worldwide. Is there a future for passwords as we know them? The answer may be simple: No. As of September 2021, Microsoft Corp. has enabled its users to remove passwords from...

by Jolera | Jun 20, 2022 | Executive Spotlight
After a successful campaign to build the European business for Jolera, CEO Alex Shan is setting the company’s sights on America. Jolera has been working in the U.S. for many years supporting channel partners and their customers, without any bricks and mortar presence....

by Jolera | Jun 9, 2022 | IT News
At the Lenovo Accelerate 2022 conference held at the Wynn Hotel in Las Vegas, Lenovo made as-a-service for the modern workforce the main theme for attendees. More than 1,500 channel partners and MSPs headed for the Las Vegas strip for one of the first in-person IT...
by Jolera | Feb 9, 2022 | IT News
Protect Your Organization from Threats and Hackers with a Security Baseline Assessment When you look at your car’s side mirrors, the sticker on the mirror will say “Objects in the mirror are closer than they appear.” This warning message is used to help drivers...

by Jolera | Jan 19, 2022 | IT News
Tick. Tick. Tick. That’s the sound of your organization getting hit with a significant breach. The coming impact of the breach depends on how quickly your organization can mitigate damage and find a solution. Acting within the first 48-hours after a breach is critical...